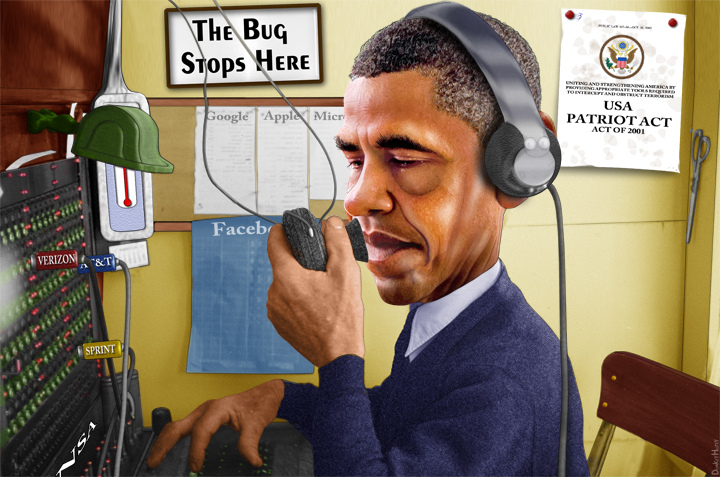
With much attention being given to the passage of the 2015 USA Freedom Act, there is some odd silence about what the bill actually contains. Pundits from every corner identify the demise of section 215 of the Patriot Act (the section that permits the government to...

NSA Reform or Foreign Policy Signaling? Maritime Provisions in Title VIII of the USA Freedom Act
read more